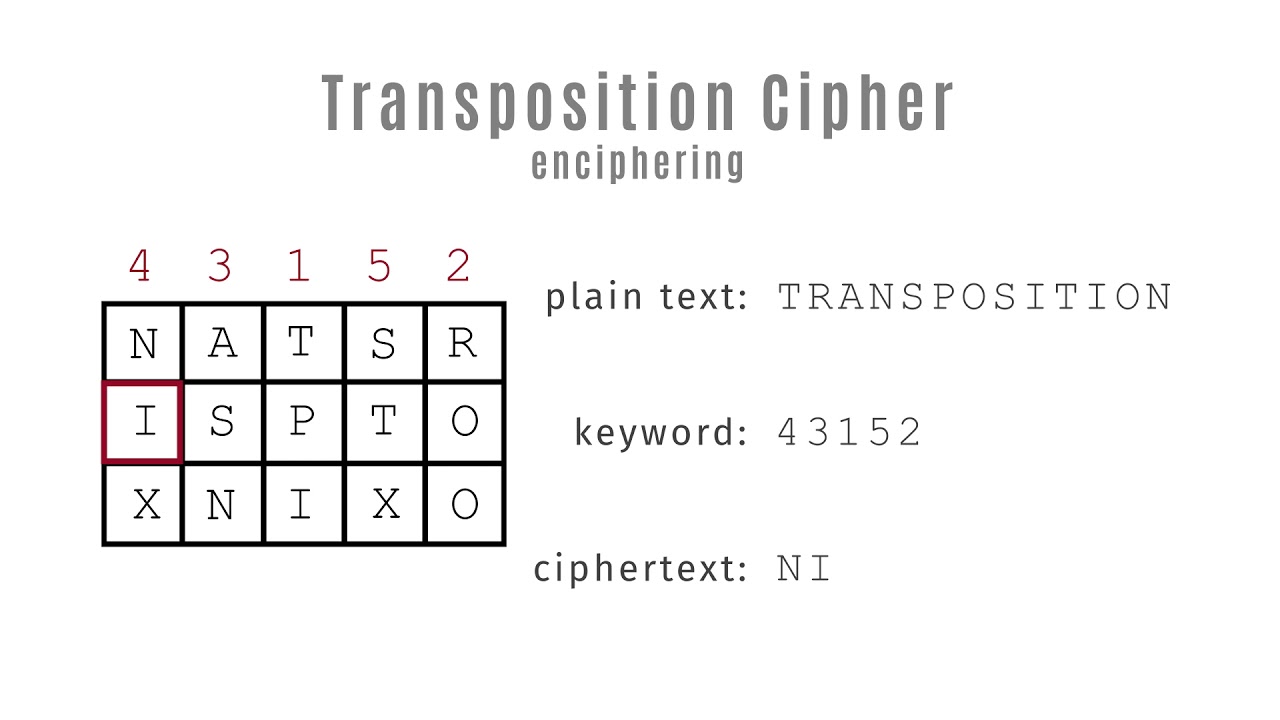
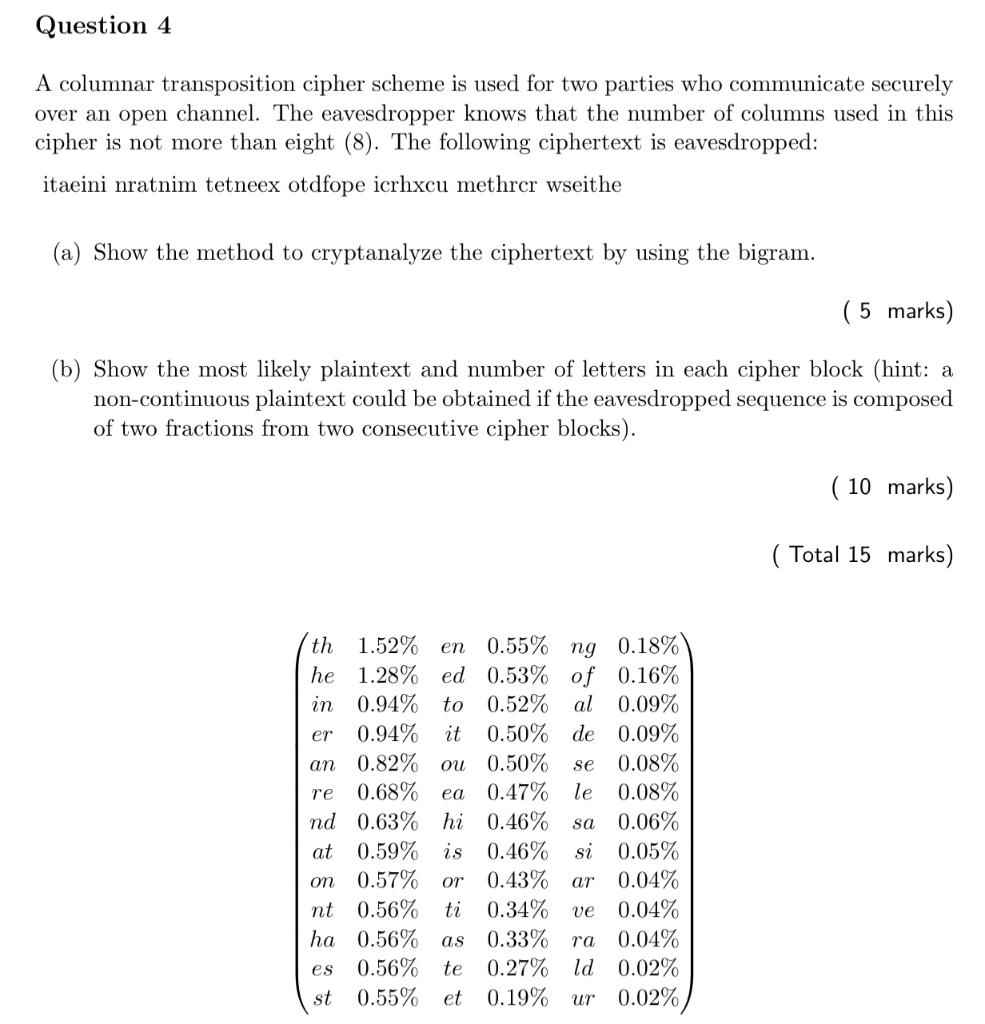
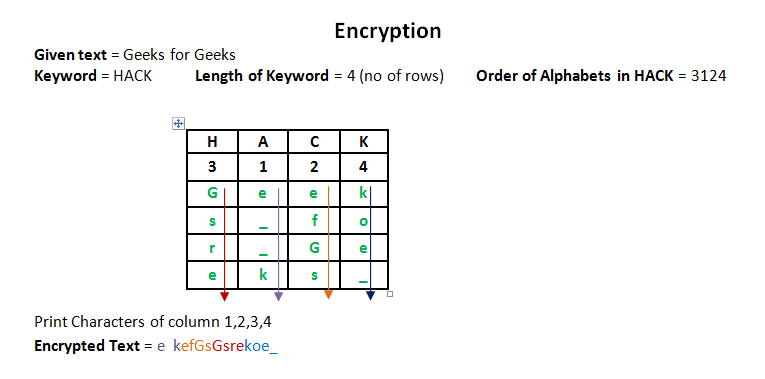
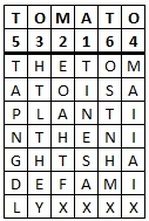
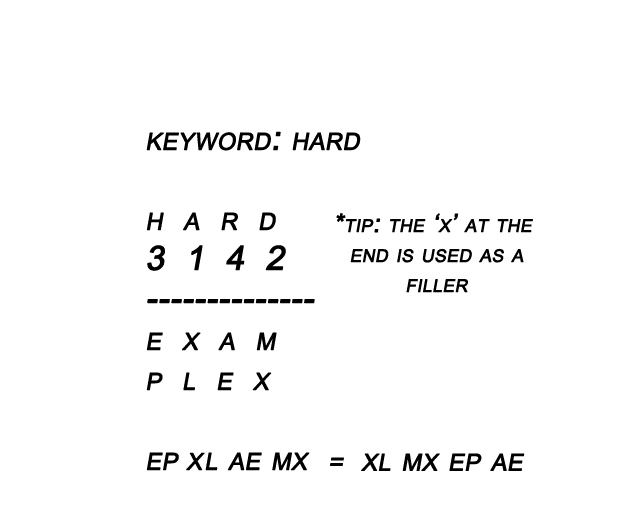
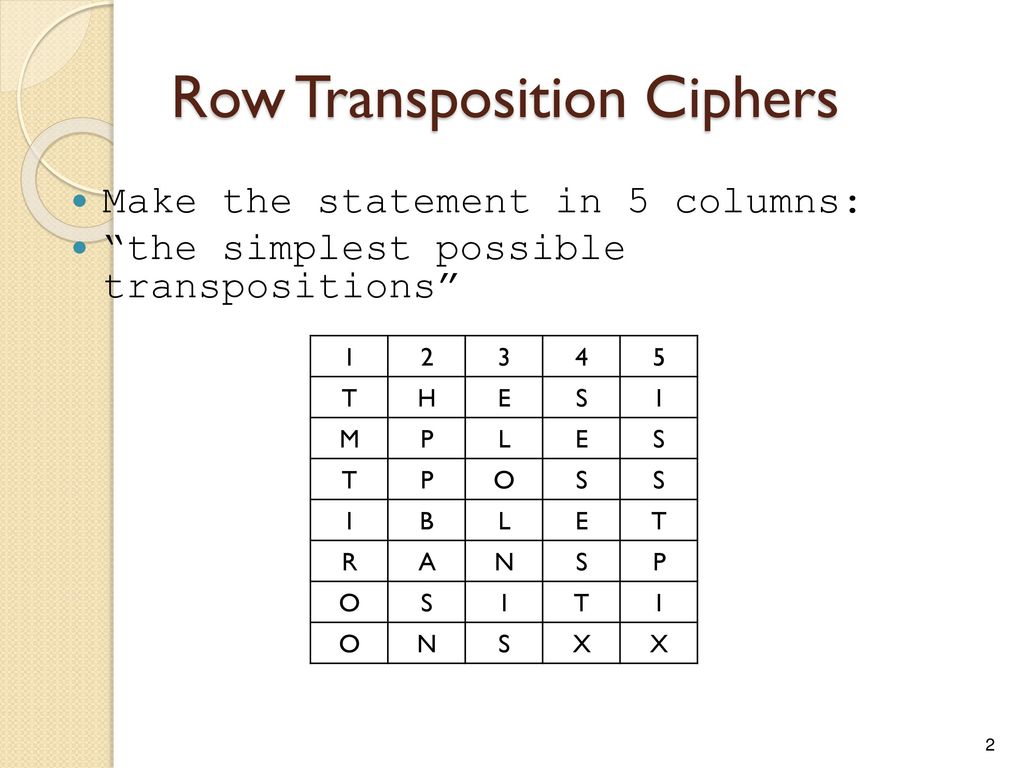
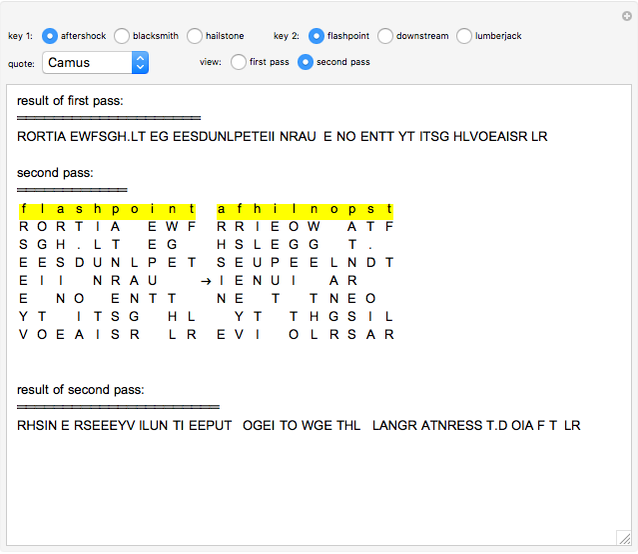
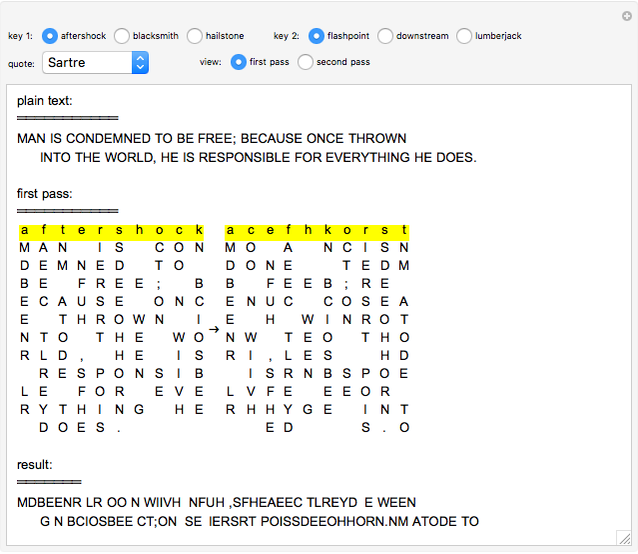
SGWEN - VII ème Caire - Columnar Transposition Cipher In a columnar transposition, the message is written out in rows of a fixed length, and then read out again column by column,

Enhancing Data Security of Columnar Transposition Cipher by Fibonacci Codes Algorithm | Semantic Scholar
![Technological information - double columnar transposition cipher in java public class Doublecoulmnar { static String encrypt(int [] key,String plain){ int col=0; for(int x=0;x<key.length-1;x++){ int temp=key[x]; if(temp<key[x+1]){ col=key[x+1]; } else ... Technological information - double columnar transposition cipher in java public class Doublecoulmnar { static String encrypt(int [] key,String plain){ int col=0; for(int x=0;x<key.length-1;x++){ int temp=key[x]; if(temp<key[x+1]){ col=key[x+1]; } else ...](https://lookaside.fbsbx.com/lookaside/crawler/media/?media_id=1036833559691384)
Technological information - double columnar transposition cipher in java public class Doublecoulmnar { static String encrypt(int [] key,String plain){ int col=0; for(int x=0;x<key.length-1;x++){ int temp=key[x]; if(temp<key[x+1]){ col=key[x+1]; } else ...

TRANSPOSITION CIPHER In the transposition technique the positions of letters/numbers/symbols in plain text is changed with one another ppt download